Troubleshooting Flow
Overview
This page provides causes of Flow monitoring problems. If necessary, read the guidelines for configuring Flow on a device, and setting up Flow in Highlight.
Background to Highlight Flow collection
- The Flow Collector sends results to Highlight every 10 minutes
- Highlight summarises results every hour on the hour
- There is an option when viewing "today" to view the 6 most recent 10 minute summaries
- The number below the Flow chart is the start time, so "8" represents 8am - 9am
Symptom 1. No Flows yet showing for any location
Firstly, check that the target Flow Collector is enabled for use from the folder/location. Contact us to confirm that the Flow Collector is responding correctly and assigned to the folder required.
Next, check that UDP port 9996 is allowed from the source device to the Flow Collector. Refer to your firewall team to confirm.
Finally, confirm that there is a route from the source device to the collector by pinging the collector IP address.
If still a problem contact us for further assistance.
Symptom 2. Router configured but no Flow reported
To confirm which devices are not reporting Flow, run an Admin watch report and check which Flow entries have no recent data.
To determine if any flow packets are being received by the Flow collector from a particular device, go to Edit watch, Applications tab, and click . This will give a list of all flows from every source address received by the Flow collector.
Check the sources against the list of IP addresses on the router.
It may be that Highlight has not been configured to match the settings on the router. For ease of comparison, look at the results of the following router commands:
show ip flow export
show ip flow interface or for Flexible Netflow use a combination of the following:
show flow monitor
show flow exporter
show flow exporter statistics
show flow interface
Confirm that:
- Today is viewed in Highlight rather than week or month view after setting the watch to monitor Flow
- For flexible or v9 implementations, the device is sending Flow templates. In these versions, the Flow data is exported in separate packets to the templates which can cause problems in data processing.
- The export destination in the device configuration is that of the Flow collector, and the port is 9996
- The IP source of the Flow packets is defined in Highlight, in the Edit watch Application tab. Note: Flow source must be an interface with an associated IP address. A physical interface with no IP address will not work.
- The interface configured with ip Flow ingress is listed and techtested in the Edit watch Application tab
ip route-cacheis configured on the router- there is no other Highlight entry using the same combination of Flow source IP address and Flow-monitored interface in the Edit watch Applications tab. For users with permission "View 'Admin' reports" this can be checked by downloading a Watch report on the Reporting Network page.
- For Juniper J-Flow ensure that the .0 sub-interface is selected rather than the physical interface which has the configuration. For example if interface fe-0/0/0 has the sampling configuration, select fe-0/0/0.0 from the list on the Applications tab.
Symptom 3. Flow monitoring showing in one direction
The likely cause of this depends on whether Flow version 5 is defined or Flow version 9.
Flow version 5
- Ensure
ip flow ingressis defined on all active interfaces
Flow version 9
- Ensure
ip flow ingressandip flow egressare defined on the monitored interface for Flow.
Alternatively if the device being monitored has only one interface connected (e.g. a newly installed device), traffic sourced from the router is not included in the exported Flow records so there is no outbound traffic reported.
Symptom 4. Flow monitoring showing high traffic
Flow on Cisco ASA
Double counting?
The issue arises because Cisco include all bytes sent and received in separate "teardown" events, which are automatically included by use of the all parameter in the configuration below. This is in addition to the periodic byte count updates. Specifying which events are to be sent eliminates the double counting. The suggested solution involves a small reconfiguration change on the ASA, as follows.
If the flow collector is using IP address N.N.N.N then try changing the config from:
policy-map global_policy
class flow_export_class
flow-export event-type all destination N.N.N.N
to:
policy-map global_policy
class flow_export_class
flow-export event-type flow-create destination N.N.N.N
flow-export event-type flow-denied destination N.N.N.N
flow-export event-type flow-update destination N.N.N.N
Wrong interface selected
- Ensure the monitored interface for Flow matches that in the Main tab. See step 4 on the Flow configuration page
Flow version 5
This symptom has been seen when Flow version 5 is defined.
- Ensure
ip flow egressis removed on all interfaces in order to avoid double counting - Alternatively change device configuration to use Flow version 9
Symptom 5. Flow monitoring showing low traffic
Flow monitoring on Cisco ASA
Assuming the selected Flow interface in Highlight matches that on the Main tab, Flow volumes would typically be less than Link Health volumes for the following reasons:
- The ASA compiles Flow records from processed traffic passing through it, so excludes any layer 2 transmission overhead being included by Link Health
- No Flows terminating on the ASA are included, for example Highlight monitoring traffic or Flow packets sent to the collector
- Conversations to be included in Flow records from an ASA could be filtered using an access-list
Flow monitoring on other devices
- If Flow analysis and Highlight Link Health monitoring have different interfaces selected then there is no direct comparison of volumes.
- (Flow version 5) Ensure
ip flow ingressis defined on all interfaces carrying traffic - (J-Flow) Check the sampling rate. For example if using 1 in 20 packets then the volumes reported would be about 5% of that possible.
Symptom 6. Standard Flow commands do not work on the router
- Try the Flexible Netflow configuration page
Symptom 7. Flow monitoring stops
If Flow analysis stops for a single device but for no obvious reason, this can be caused by a router change, either replacement or configuration, which has altered the number of the interface being monitored. The solution for this is:
- Reselect the Interface to be monitored for Flow in the Applications tab of the device
- Also if an additional interface has been added to the router and to avoid a recurrence of this symptom then add the following device configuration for interface persistence:
snmp-server ifindex persist
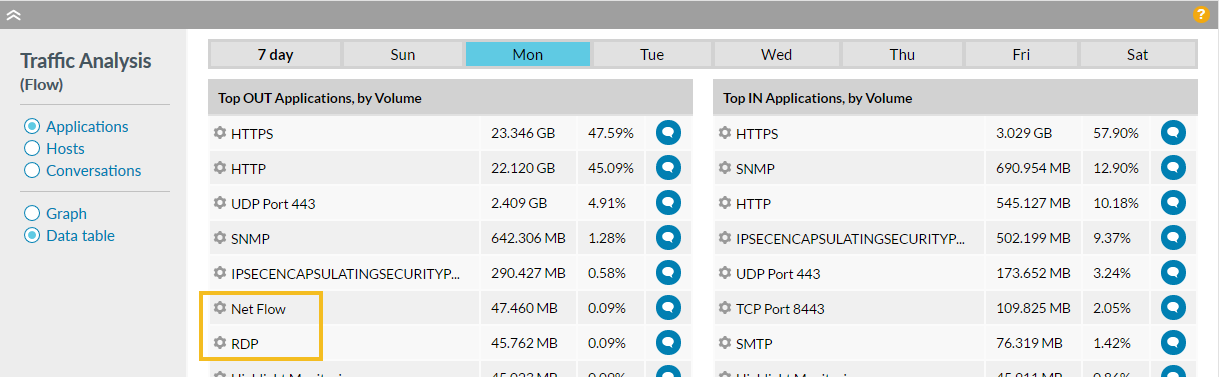
Symptom 8. Day Flow breakdown differs from weekly breakdown by day
- This is standard behaviour.
Day view shows the top 20 applications or hosts in that day.
Week view by day displays the applications/hosts from the week's top 20 which were seen on the day in question.
Daily Flow summary for Monday
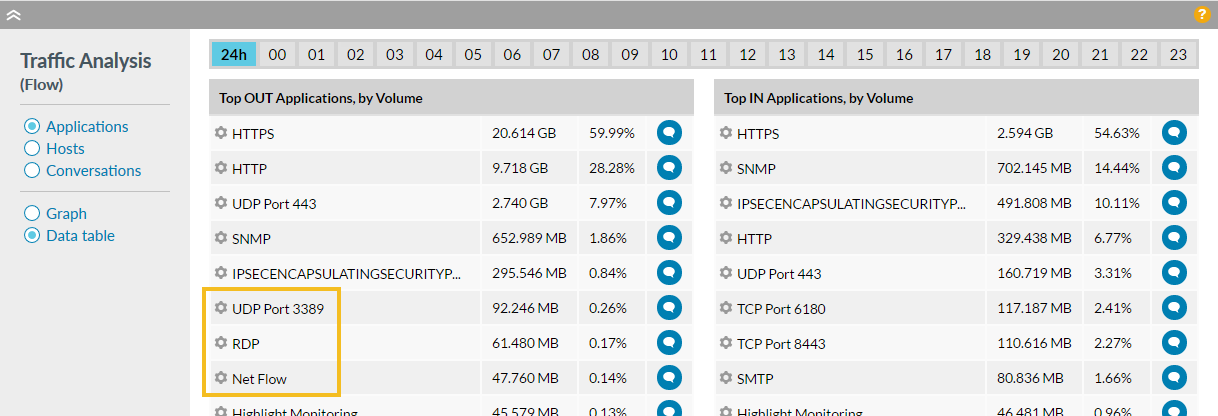
Weekly Flow summary, broken down for the Monday
Additional Troubleshooting
If there is no success following the points above, it is likely to require access to the Flow Collector to check the logs and/or run a packet capture. Contact us for further assistance.